Router exploit leaves millions vulnerable
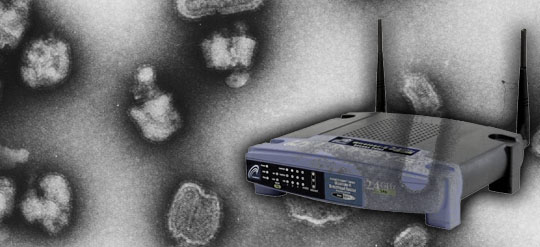 One of the biggest problems with computer security has to do with password protection. Although it took a few years, most users are now smart enough to make sure they have proper password protection both on their computers and their WiFi, but a new variation of an old exploit appears to leave a wide range of consumer grade routers vulnerable to attack
One of the biggest problems with computer security has to do with password protection. Although it took a few years, most users are now smart enough to make sure they have proper password protection both on their computers and their WiFi, but a new variation of an old exploit appears to leave a wide range of consumer grade routers vulnerable to attack
The exploit, reported by Ars Technica, and to presented at the Black Hat security conference as “How to Hack Millions of Routers”, is a new take on an old hack known as DNS rebinding, which allows a malicious user to change the DNS settings on a router, so that the unsuspecting user is redirected to a different page than the one they expected when they surf. What makes this especially tricky is that if you are hacked, you may be directed to a page that looks like your banking site, but instead it’s a page used to get your account and password information for nefarious means.
What’s really surprising is that even routers with custom firmware, such as the popular Tomato software, are vulnerable to the attack, and many routers, even with a new password, are flawed enough that there are ways to bypass that protection. The Ars article has much more in the way of details, as well as a list of some of the more popular routers that are vulnerable. If the last column says “Yes” then the router is vulnerable. The only major router maker that seems to come away unscathed, in the tested models anyways, is DLink.
I wouldn’t say it’s time to panic or buy a new router, but if you’ve never changed the password on your router, security issues like this are always a good reminder.
[source]




[…] This post was mentioned on Twitter by Doug Groves, Jon. Jon said: Router exploit leaves millions vulnerable: If the last column says “Yes” then the router is vulnerable. The only m… http://bit.ly/bFXm8R […]